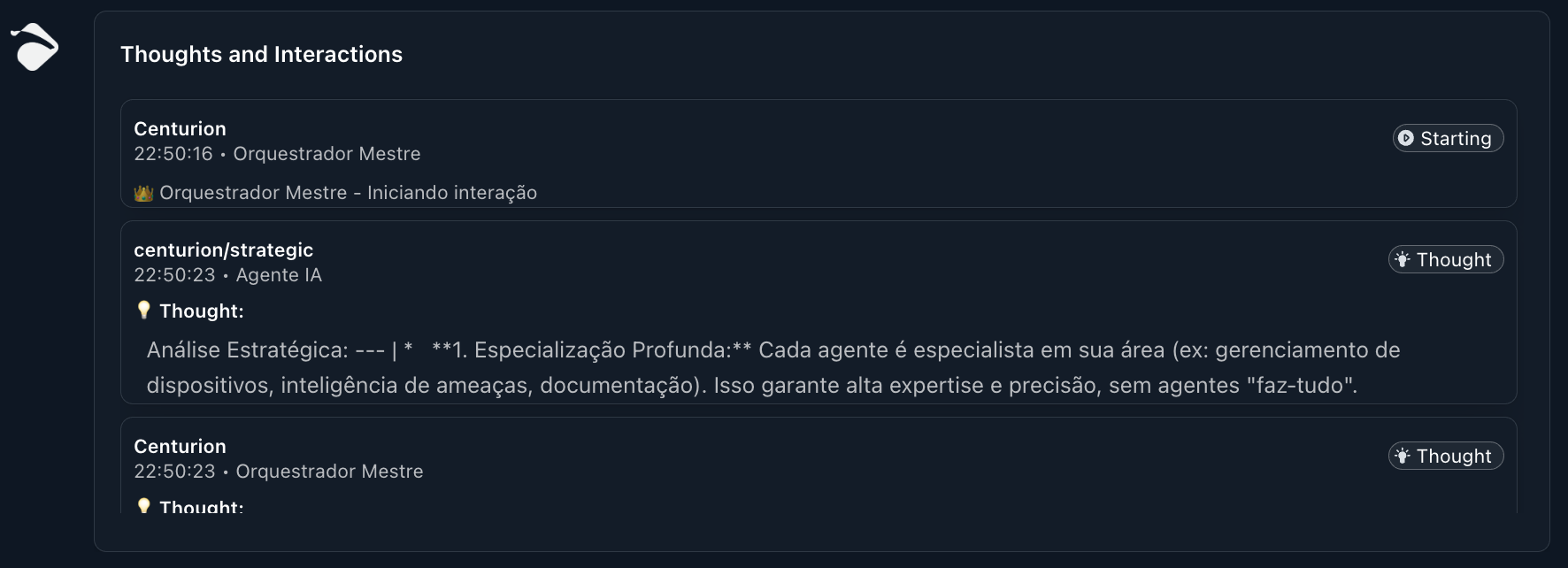
Benefits of the Multi-Agent Architecture
Adopting a multi-agent architecture offers significant advantages, translating into a more robust and effective security platform:- Deep Specialization: Each agent is an expert in its specific domain (e.g., endpoint management, threat intelligence, documentation). This ensures that every task is executed with the highest level of expertise and precision, without the need for a generic “jack-of-all-trades” agent.
- Resilience and Robustness: The modularity of the architecture means that the failure or maintenance of one agent does not compromise the operation of the entire system. Centurion can, in many cases, adapt the strategy or reallocate tasks, ensuring service continuity.
- Efficient Scalability: The platform can be easily scaled by adding new specialized agents or expanding the capabilities of existing agents, without the need for re-engineering the entire system. This allows Myrmex to grow and adapt to the constantly evolving demands of the threat landscape.
- Operational Efficiency: Distributing tasks among agents enables parallel processing and simultaneous execution of different aspects of a request. This optimizes response time and resource utilization.
- Adaptability and Flexibility: The architecture allows the platform to quickly adapt to new technologies, threats, and security requirements. New agents can be integrated to address emerging challenges while maintaining system cohesion.
- Collective Intelligence and Synergy: The collaboration between agents, orchestrated by Centurion, generates an intelligence that is greater than the sum of its parts. The ability to combine insights from different domains (e.g., device data, external intelligence, security events) results in deeper analyses and more informed decisions.
Demonstrating Collaboration: Practical Examples
The true strength of the Multi-Agent architecture lies in the agents’ ability to work together, under Centurion’s coordination, to solve complex problems.Example 1: Comprehensive Security Incident Response
Imagine a scenario where a threat entry is identified in your environment. Centurion, as the strategic brain, immediately evaluates the situation and orchestrates the following response:Initial Detection & Contextualization
Centurion
Receives the alert and analyzes the situation
Iris
Searches for external threat intelligence and related IoCs
Device Analysis and Identification
Perseus
Under Centurion’s command, Perseus identifies the affected server and collects detailed live telemetry (OS, running services, security configurations)
Forensic Investigation and Impact Analysis
Perseus
Extends Centurion’s intelligence to perform in-depth analysis: checking events, running processes, and active network connections to determine the extent of the threat.
Threat Intelligence and Attribution
Orion
Analyzes collected IoCs to attribute the threat to a specific actor group or campaign, providing crucial information for the response
Mitigation and Containment
Hydra
Executes the orchestrated containment: Centurion directs Hydra to block malicious IPs on firewalls or isolate compromised segments via API.
Example 2: Proactive Security Posture Assessment and Recommendations
For continuous security posture assessment, the collaboration would be as follows:Inventory and Baseline
Perseus
Maintains an updated inventory of all network devices, monitoring their configurations and status
Vulnerability Analysis
Orion
Monitors for new vulnerabilities (CVEs) and correlates them with Perseus’ inventory to identify potentially vulnerable devices
Perseus
Analyzes device configurations for security policy deviations
Hardening Recommendations
Centurion
Formulates hardening recommendations based on analyses from Perseus and Orion
Hydra
Suggests and applies optimized firewall configurations, IPS policies, or network segmentation for network devices like Fortigate FGT-NM