It understands your needs
From device management to complex threat analysis, Myrmex comprehends what
needs to be done.
It orchestrates action
Instead of having to manage multiple tools and teams, Myrmex automatically
coordinates its specialized agents to execute security tasks in an
integrated and effective manner.
It provides intelligence
Collects and analyzes security data from various sources, transforming them
into actionable information so you can make quick and informed decisions.
How Does Myrmex Work?
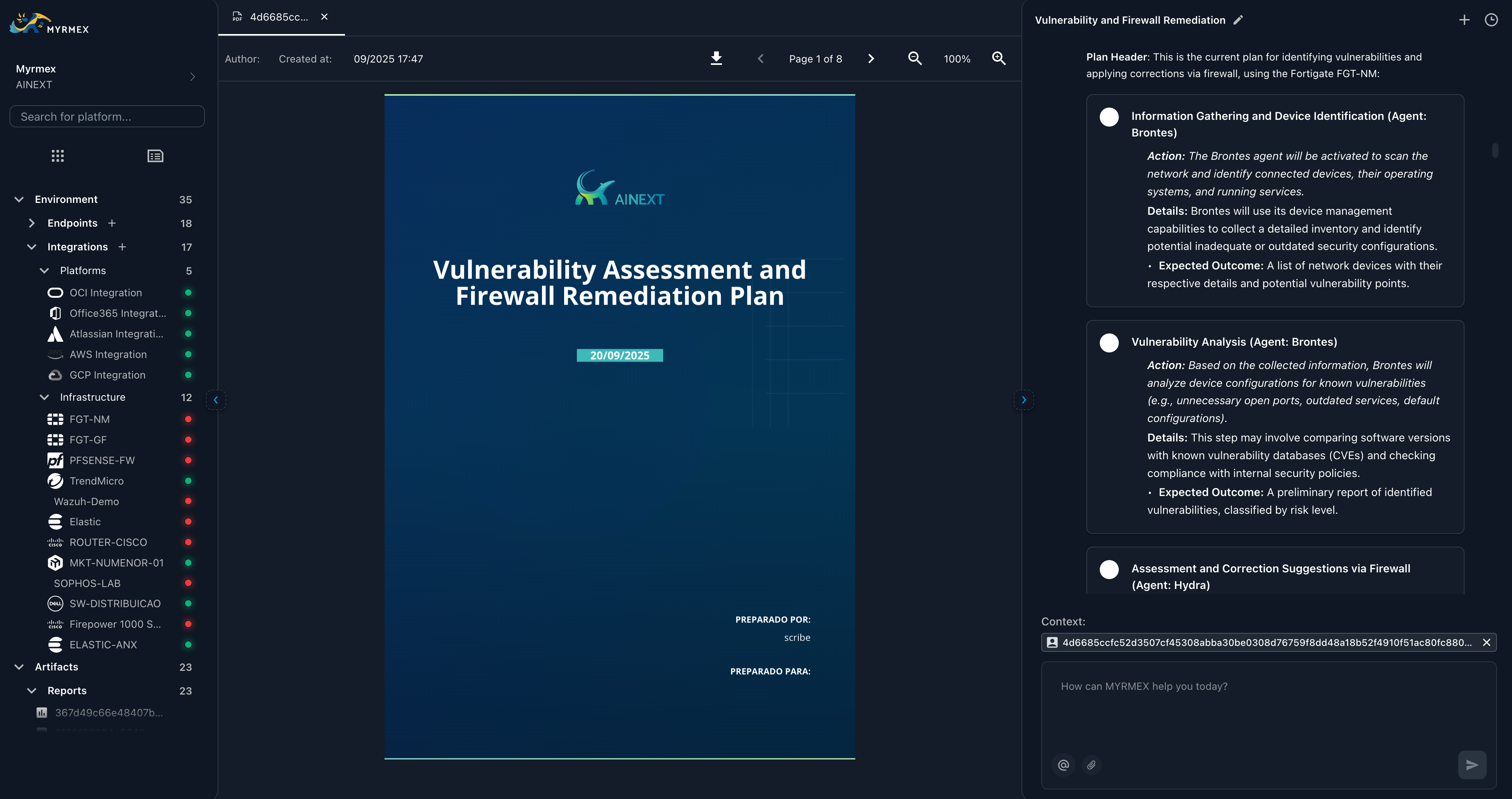
At the heart of Myrmex is Centurion, the master orchestrator. Centurion is the artificial intelligence that receives your requests and distributes them to the most suitable agents. Each Myrmex agent is a specialist in their area:Centurion
The master orchestrator and chief intelligence coordinator. Centurion is the brain of your cybersecurity operations, transforming complex challenges into strategic plans and directing specialized agents to execute them seamlessly.
Perseus
The Endpoint Specialist arm. Under Centurion’s command, Perseus manages device inventory and health, while executing precision technical operations and orchestrated remediation across your fleet.
Hydra
The Integration arm. Centurion utilizes Hydra to coordinate actions across security platforms (firewalls, cloud, etc.), ensuring your entire ecosystem is part of an orchestrated defense strategy.
Iris
Researches information and external intelligence on the internet. Acts like
a smart and fast private detective performing online investigations and website analysis.
Orion
Investigates threats and provides reconnaissance intelligence. Offers
advanced threat analysis, compromised email detection, and vulnerability assessments.
Scribe
Creates professional reports and documentation. Generates comprehensive
security reports, incident documentation, and maintains security knowledge base.
Why is Myrmex Essential for Your Security?
Simplifies Complexity: Transforms complex security tasks into automated and easy-to-manage processes. Increases Efficiency: Reduces incident response time and optimizes security operations. Strengthens Defense: Provides a comprehensive and proactive view against cyber threats. Adapts to Your Needs: Whether you’re an individual professional, a small business, or a large corporation, Myrmex adjusts to protect what matters most to you.Getting Started
Quick Start
Learn the basics and start using MYRMEX
Concepts
Get started with MYRMEX concepts
Access Control
Manage team roles, permissions, and security policies (IAM)